30
Jun 2020
Dental Office Cybersecurity Fails
If I’ve seen it once, I’ve sent a thousand emails about it. Our typical client is somewhere around 10-25 computers with a couple servers and a bunch of network gear. Most commonly, we see non-profit organizations, retail stores and dental offices. In this blog post, we’re going to outline the 3 unmistakably most common dental office cybersecurity fails that we see on a monthly weekly basis.
The first one is easy.
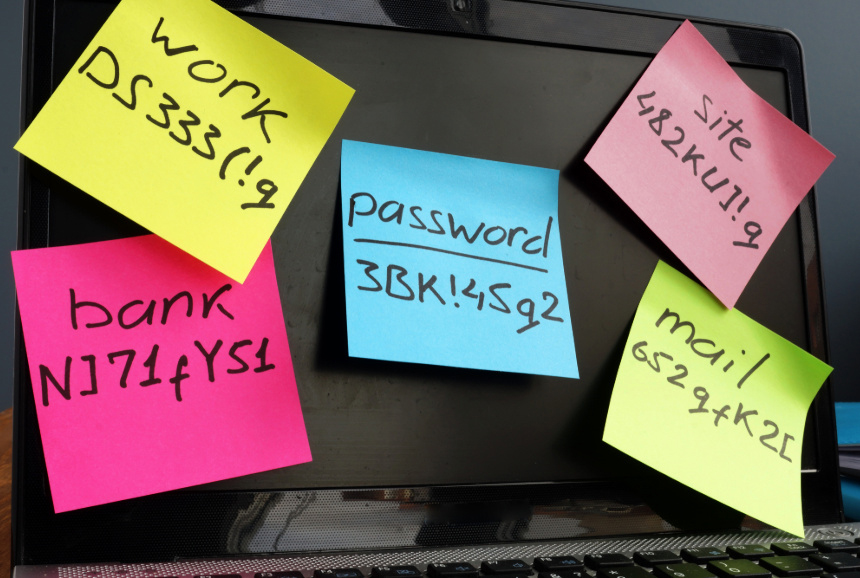
Go have a quick walk around the office. Are there sticky notes containing usernames and passwords on monitors, under keyboards, behind the front desk cabinets or inside cabinet doors?
Go ahead – I’ll wait.
1 – Sticky Note Passwords
Yes, it’s the constant battle between IT and the end user. Those pesky techs are always demanding passwords that expire over a set number of days (which, by the way, isn’t the recommended norm anymore) or other password security standards that are sometimes hard to comply with.
Most of all, good passwords are usually hard to remember.
Okay – so here’s how you can fix that.
A password schema is pretty easy to make, it’s unique and it should comply with most security standards. Here’s what you’re going to do;
- Pick a symbol. We’ll use ‘#’ for this example.
- Next, take the first 4 letters of the service you’re trying to access in lower-case. For this example, we’ll use ‘goog’ and pretend we’re logging into Google.
- Next, slap a good password on that string. A good password uses 8-12 characters. Let’s say our password is QuickBrownFox
- Lastly – tag a set of meaningful numbers on the end, like the last 4 digits of your business phone number. So, for us, we would use 4098.
Boom – you’ve got a password (#googQuickBrownFox4098) that is different for every service you’re logging into and damn hard to crack.
If you’re not into that – try a password manager. Better than that, try an enterprise password manager like the one we’re saddled up with. Contact us for a free trial.
2 – Untested Backups
Yes – backups are a part of your dental office cybersecurity stack.
No – that USB key your IT guy set up 6 years ago isn’t good enough.
A solid backup strategy should follow the industry standard ‘3-2-1 rule’. So, your mission critical data should have 3 copies in 2 physical locations with 1 of them being offsite.
Take all your data (records, accounting, archives) and send it to an offsite backup provider. Also get it replicated to an on-site storage device like a NAS. If you need help with that process, I know a guy.
3 – Set it and forget it AV
More often than not, the small business market is flooded with quick-set appliances that are marketed as catch-all solutions for every known threat. If you’re running an Anti-Virus client and nothing else, that is the equivalent of wearing a helmet while you unicycle into Mordor.
Anti-virus was heavily marketed in the 90’s as the saving grace for regular internet users. The simple fact is, however, it just isn’t enough.
Think of your cybersecurity efforts like layers of an onion – the more layers, the better. These layers are commonly referred to as your ‘stack’.
As far as we’re concerned, the very first layer of your stack – well before Anti-Virus programs, is end-user education. The people answering emails, picking up the phone and talking to the delivery guy are your front line of defense against cybersecurity threats. They’re the ones who have to parse through the bad attachments your e-mail provider misses. They’re the folks who question that little feeling in their gut about the legitimacy of a phishing attack. Those people – not computers – are the eyes and ears of your network.
At the very least, they should be equipped with the ‘see something, say something’ backbone of end-user education.
Too often, I see small businesses under the lock and key of the owner. In work cultures where employees are nervous to speak up, hackers win.
Most times, it’s a matter of breaking down the technical newsbytes into more easily digestible and relatable ideas.
Turns out, we’re pretty good at that, too – give us a shout for a free cyber security workshop at your next staff meeting.
Bringing your office up against the wild-west of the dental office cybersecurity landscape is simple, not easy. It’s an ongoing campaign, not a destination. It requires dedication, discipline and a determined effort to be better.